Heap Spraying: Introduction
In past several months, Heap spraying has become one of the most prevalent technique to exploit vulnerability in browser. IE “createTextRange()” and Mozilla Firefox “InstallVersion.compareTo()” are the examples of this technique. Because it is undocumented technique – actually not well document, I decide to start to study what is it and how it work.
This technique was introduced by hacker named “SkyLined”. He used Heap Spraying technique to attack the vulnerability in IE, MS04-040 and MS05-020. However I also found the technique like heap spraying, it was mentioned in Microsoft Internet Information Services Remote Buffer Overflow.
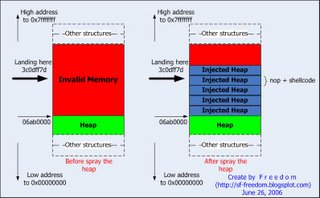
After I had read these exploit codes, I got some point about this technique. Heap spraying is used when the vulnerable program (IE, Firefox in this case) call or jmp into invalid memory. This invalid memory must be in the possible heap range address - not in DLL virtual address, PEB, TEB, etc. And it must not higher than 0x7fffffff because above this address is kernel address space. See
Windows Memory Layout for detail. This is one of the limitation of heap spraying technique.
So, what can we do if it jumps into the possible heap range but invalid memory? The answer depends on the nature of the vulnerable program. If we can't control (actually "injected") the application's heap - Gave Over. But if we can, we will inject heap as much as possible until the invalid memory become the valid memory. Sure, the injected heaps contain our nop + shellcode, so the vulnerable program will landing on our nop and shellcode :) That's why this technique is called "Heap Spraying"
Now, I got another limitation of this technique - we have to able to control the application's heap. As I known, there are few applications that we are able to control heap. Web browser is the one of these - inject heap via JavaScript
I also create a simple picture to demonstrate the basic concept about it. Here's the picture.
Even though heap spraying concept is the simple one, its implementation quite complex. There are many things I must to find out...

4 Comments:
Ni-hao Lao-sui
Jeng dee ah
By Anonymous, at June 30, 2006 11:50 PM
Anonymous, at June 30, 2006 11:50 PM
pls check ur photos in ur blog! thanx
By Anonymous, at September 26, 2006 6:10 AM
Anonymous, at September 26, 2006 6:10 AM
picture link address mismatch
By Anonymous, at November 16, 2006 4:11 PM
Anonymous, at November 16, 2006 4:11 PM
Thanks for your work, it is much appreciated.
By Anonymous, at August 19, 2007 12:48 AM
Anonymous, at August 19, 2007 12:48 AM
Post a Comment
<< Home